Mitsubishi claims that the technology is the first to define detection rules based on the normal commands for control systems and to interpret deviations from these commands as an attack. The technique can maintain the real-time operation of control systems under attack because it does not involve a time-consuming process of making comparisons with suspicious patterns.
Mitsubishi adds that the technology will contribute to infrastructure stability by reducing detection times, and minimising any effects on control-system processes that must finish within certain time limits.
The company reports that there have been cases of advanced cyber-attacks penetrating control systems to issue commands that pretend to be normal and are difficult to distinguish from real commands. Existing detection methods that compare incoming traffic with known suspicious patterns can fail to detect such attacks. Comparing the network traffic with the enormous volume of known suspicious patterns take times and can cause real-time control systems to fail.
Mitsubishi noticed that normal control-system traffic in critical infrastructure installations can differ depending on whether the system is operating, not operating or is undergoing maintenance – so the new technology uses different detection rules for each of these operational states.
With cyber-attacks continuing to increase, it takes an enormous amount of time to generate suspicious patterns and to search for matches with these patterns. But there are only a limited number of normal commands used in control systems, so the detection rules can be limited to look for these commands, enabling the new technology to search for matches and to detect attacks rapidly, while maintaining the real-time operation of control systems.
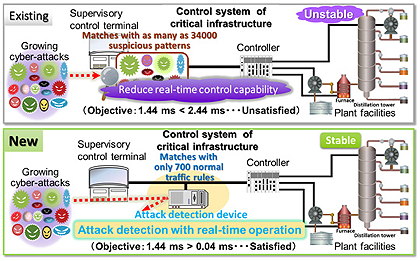
Existing cyber-attack detection systems (top) take too long to perform pattern-matching tasks, risking the disruption of real-time control systems. The new approach (bottom) checks against a limited number of normal commands, and can therefore detect attacks before they can disrupt the operation of the control systems.
Mitsubishi measured to time taken to detect an attack on one control system and found that the new technology took just 0.04ms, compared to 2.44ms for an existing alternative. To maintain real-time operation in the control system, the maximum allowable detection time was 1.44ms.
The new technology is based on the results of a project undertaken by Japan’s Control System Security Centre (CSSC), and commissioned by the country’s New Energy and Industrial Technology Development Organisation (Nedo).
Mitsubishi plans to commercialise the cyber-attack detection technology in 2018, starting with applications for electric power infrastructures. Other applications will be developed in collaboration with Japan’s Strategic Innovation Promotion Program (SIP) challenge for the cyber-security of critical infrastructure.

